Tor is free software that prevents people from learning your location or browsing habits by letting you communicate anonymously on the Internet. This article outlines the process of installing TOR and shows how to communicate through the TOR network by using the Python programming language.
Installing TOR Proxy on port 9050
On Linux (RHEL/FEDORA/Centos)
The Tor installation on Linux is a fairly simple process, just execute the following two commands to install and enable the service: yum install tor (to install Tor service) systemctl start tor (to start Tor service) Windows
If you're on Windows, simply install the extended bundle (not browser installation) directly from the following URL: https://dist.torproject.org/torbrowser/8.5a11/tor-win64-0.4.0.4-rc.zip. Then unzip it go to Tor install directory, usually: C:\tor-win64-0.4.0.4-rc\ and run the command prompt as Administrator, from the C:\tor-win64-0.4.0.4-rc\Tor directory, to install and start the service, like this:
tor --service install -options ControlPort 9051
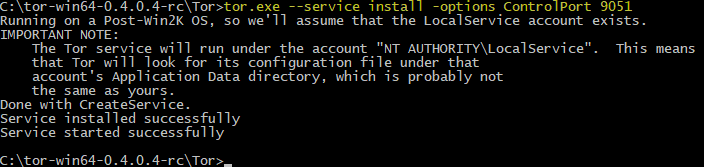
Once done, Tor will create a proxy at http://localhost:9050 and ControlPort on 9051 port, allowing you to receive and forward traffic from your computer to Tor network nodes.
PYTHON CODE
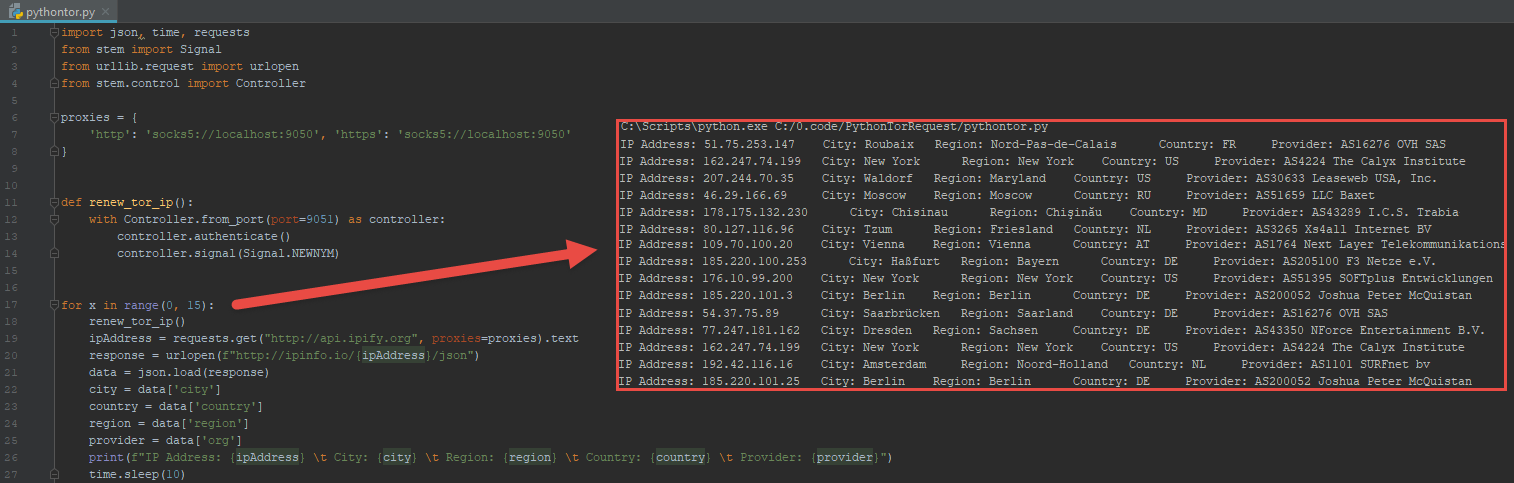
Here is a short Python script that:
- Obtains a connection from the TOR network
- Uses the connection as a proxy through which we'll flow our Internet requests.
- Then the script obtains the IP Address from [http://api.ipify.org](http://api.ipify.org) service which provides us with the IP address of the computer through which we're connecting to the Internet.
- And to make it a little more interesting, we'll leverage the [http://ipinfo.io](http://ipinfo.io) service to add the geolocation information for the TOR computer we're using as a proxy. The information such as the city, region, country and also the Internet provider of our connecting TOR node.
This is what the Python script looks like and as you'll see, it's very self-explanatory. First, we defined the proxy location of the TOR service installed on our computer or server. Then there is a single function that requests the new node from the TOR network, which is eventually used prior to sending the 'what's my ip address' request.
import json import time import requests from urllib.request import urlopen from stem import Signal from stem.control import Controller
proxies = { 'http': 'socks5://localhost:9050', 'https': 'socks5://localhost:9050' }
def renew_tor_ip(): with Controller.from_port(port=9051) as controller: controller.authenticate() controller.signal(Signal.NEWNYM)
for x in range(0, 15): renew_tor_ip() ipAddress = requests.get("http://api.ipify.org", proxies=proxies).text response = urlopen(f"http://ipinfo.io/{ipAddress}/json") data = json.load(response) city = data['city'] country = data['country'] region = data['region'] provider = data['org'] print(f"IP Address: {ipAddress} \t City: {city} \t Region: {region} \t Country: {country} \t Provider: {provider}") time.sleep(10)
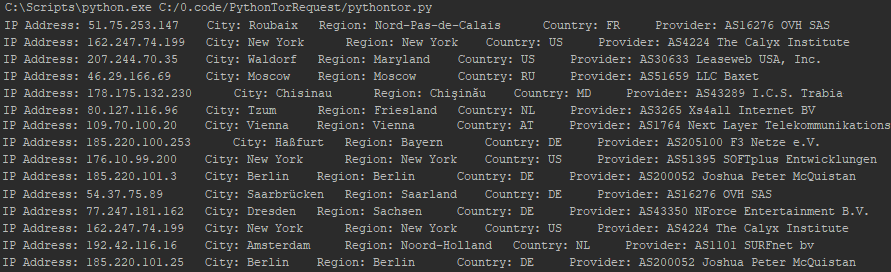
I've coded the script to run the 15 loops and as we can see, my traffic is anonymous, with practically every request coming from a different country. In a span of a minute or so, our Python script connected to internet through 15 x unique TOR nodes , located in France (Roubaix), USA (New York, Waldorf), Russia (Moscow), Moldova (Chisinau), but also in Netherlands (Tzum, Amsterdam), Austria (Vienna) and Germany (Habfurt, Saarbrucken, Hamburg and Berlin).
Screenshots:
Let me know if you find this useful.
The source https://github.com/JozefJarosciak/PythonTorRequest/